crypto key generate rsa
To generate Rivest, Shamir, and Adelman (RSA) key pairs, use thecryptokeygeneratersacommandinglobal configuration mode.
cryptokeygeneratersa [ general-keys| usage-keys| signature|encryption ] [ labelkey-label ] [exportable] [ modulusmodulus-size ] [ storagedevicename: ] [redundancy] [ ondevicename: ]
Syntax Description
The crypto key generates RSA command is something that will be dependent on the IP domain name commands and the hostname. The crypto command can be used in order to generate a key pair which will have a private and public RSA key. Based on the given choices, the right answer to this question is C because you can get a key pair whenever this.
general-keys | (Optional) Specifies that a general-purpose key pair will begenerated, which is the default. | ||
usage-keys | (Optional) Specifies that two RSA special-usage key pairs, oneencryption pair and one signature pair, will be generated. | ||
signature | (Optional) Specifies that the RSA public key generated will be asignature special usage key. | ||
encryption | (Optional) Specifies that the RSA public key generated will bean encryption special usage key. | ||
labelkey-label | (Optional) Specifies the name that is used for an RSA key pairwhen they are being exported. If a key label is not specified, the fully qualified domain name(FQDN) of the router is used. | ||
exportable | (Optional) Specifies that the RSA key pair can be exported toanother Cisco device, such as a router. | ||
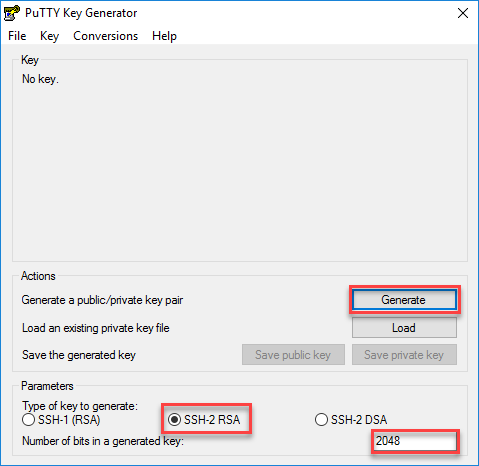
modulusmodulus-size | (Optional) Specifies the IP size of the key modulus. By default, the modulus of a certification authority (CA) key is1024 bits. The recommended modulus for a CA key is 2048 bits. Therange of a CA key modulus is from 350 to 4096 bits.
| ||
storagedevicename: | (Optional) Specifies the key storage location. The name of thestorage device is followed by a colon (:). | ||
redundancy | (Optional) Specifies that the key should be synchronized to thestandby CA. | ||
ondevicename: | (Optional) Specifies that the RSA key pair will be created onthe specified device, including a Universal Serial Bus (USB) token,local disk, or NVRAM. The name of the device is followed by a colon(:). Keys created on a USB token must be 2048 bits or less. |
Router1# configure terminal Enter configuration commands, one per line. End with CNTL/Z. Router1 (config)# crypto key generate rsa The name for the keys will be: Router1.oreilly.com Choose the size of the key modulus in the range of 360 to 2048 for your General Purpose Keys. Choosing a key modulus greater than 512 may take a few minutes. While reconfiguring a Cisco switch 3750G WS-C3750G-24TS-S1U with version 12.0(5.3). When attempting to run “crypto key genearte rsa“, it was failing with below error: MW-CORE-SW01#conf tEnter configuration commands, one per line. End with CNTL/Z.MW-CORE-SW01(config)#hostname MWiredMW-CORE-SW01(config)#ip domain-name magwinya.co.zaMW-CORE-SW01(config)#crypto key generate rsa% Invalid input.
Command Modes
Global configuration
Command History
Release | Modification |
|---|---|
11.3 | This command was introduced. |
12.2(8)T | The key-label argumentwas added. |
12.2(15)T | The exportable keyword was added. |
12.2(18)SXD | This command was integrated into Cisco IOS Release12.2(18)SXD. |
12.4(4)T | The storagekeyword anddevicename: argument were added. |
12.2(33)SRA | This command was integrated into Cisco IOS Release12.2(33)SRA. |
12.4(11)T | The storagekeyword anddevicename: argument were implemented on the Cisco7200VXR NPE-G2 platform. The signature, encryption and on keywords and devicename: argument were added. |
12.4(24)T | Support for IPv6 Secure Neighbor Discovery (SeND) was added. |
XE 2.4 | The maximum RSA key size was expanded from 2048 to 4096 bits forprivate key operations. |
15.0(1)M | This command was modified. The redundancy keyword was introduced. |
15.1(1)T | This command was modified. The range value for the modulus keyword value isextended from 360 to 2048 bits to 360 to 4096 bits. |
15.2(2)SA2 | This command was implemented on the Cisco ME 2600X SeriesEthernet Access Switches. |
Usage Guidelines
Note | Security threats, as well as the cryptographic technologies tohelp protect against them, are constantly changing. For moreinformation about the latest Cisco cryptographic recommendations,see the Next Generation Encryption (NGE) whitepaper. |
Use this command to generate RSA key pairs for your Cisco device(such as a router).
RSA keys are generated in pairs--one public RSA key and oneprivate RSA key.
If your router already has RSA keys when you issue this command,you will be warned and prompted to replace the existing keys withnew keys.
Note | Before issuing this command, ensure that your router has ahostname and IP domain name configured (with the hostname and ipdomain-name commands). You will be unable tocomplete the cryptokeygeneratersacommand without a hostname and IP domain name. (This situation isnot true when you generate only a named key pair.) |
Cisco Crypto Key Generate Rsa Command Generator
Note | Secure Shell (SSH) may generate an additional RSA key pair ifyou generate a key pair on a router having no RSA keys. Theadditional key pair is used only by SSH and will have a name suchas {router_FQDN }.server. For example, if a router name is“router1.cisco.com,” the key name is“router1.cisco.com.server.” |
This command is not saved in the router configuration; however,the RSA keys generated by this command are saved in the privateconfiguration in NVRAM (which is never displayed to the user orbacked up to another device) the next time the configuration iswritten to NVRAM.
Note | If the configuration is not saved to NVRAM, the generated keysare lost on the next reload of the router. |
There are two mutually exclusive types of RSA key pairs:special-usage keys and general-purpose keys. When you generate RSAkey pairs, you will be prompted to select either special-usage keysor general-purpose keys.
Special-Usage Keys
If you generate special-usage keys, two pairs of RSA keys willbe generated. One pair will be used with any Internet Key Exchange(IKE) policy that specifies RSA signatures as the authenticationmethod, and the other pair will be used with any IKE policy thatspecifies RSA encrypted keys as the authentication method.
A CA is used only with IKE policies specifying RSA signatures,not with IKE policies specifying RSA-encrypted nonces. (However,you could specify more than one IKE policy and have RSA signaturesspecified in one policy and RSA-encrypted nonces in anotherpolicy.)
If you plan to have both types of RSA authentication methods inyour IKE policies, you may prefer to generate special-usage keys.With special-usage keys, each key is not unnecessarily exposed.(Without special-usage keys, one key is used for bothauthentication methods, increasing the exposure of that key.)
General-Purpose Keys
If you generate general-purpose keys, only one pair of RSA keyswill be generated. This pair will be used with IKE policiesspecifying either RSA signatures or RSA encrypted keys. Therefore,a general-purpose key pair might get used more frequently than aspecial-usage key pair.
Named Key Pairs
If you generate a named key pair using the key-labelargument, you mustalso specify the usage-keys keyword or the general-keys keyword. Namedkey pairs allow you to have multiple RSA key pairs, enabling theCisco IOS software to maintain a different key pair for eachidentity certificate.
Modulus Length
When you generate RSA keys, you will be prompted to enter amodulus length. The longer the modulus, the stronger the security.However a longer modules takes longer to generate (see the tablebelow for sample times) and takes longer to use.
Router | 360 bits | 512 bits | 1024 bits | 2048 bits (maximum) |
|---|---|---|---|---|
Cisco 2500 | 11 seconds | 20 seconds | 4 minutes, 38 seconds | More than 1 hour |
Cisco 4700 | Less than 1 second | 1 second | 4 seconds | 50 seconds |
Cisco IOS software does not support a modulus greater than 4096bits. A length of less than 512 bits is normally not recommended.In certain situations, the shorter modulus may not functionproperly with IKE, so we recommend using a minimum modulus of 2048bits.
Note | As of Cisco IOS Release 12.4(11)T, peer public RSA keymodulus values up to 4096 bits are automatically supported. Thelargest private RSA key modulus is 4096 bits. Therefore, thelargest RSA private key a router may generate or import is 4096bits. However, RFC 2409 restricts the private key size to 2048 bitsor less for RSA encryption. The recommended modulus for a CA is2048 bits; the recommended modulus for a client is 2048 bits. |
Additional limitations may apply when RSA keys are generated bycryptographic hardware. For example, when RSA keys are generated bythe Cisco VPN Services Port Adapter (VSPA), the RSA key modulusmust be a minimum of 384 bits and must be a multiple of 64.
Specifying a Storage Location for RSA Keys
Cisco Router Crypto Key Generate Rsa Command
When you issue the cryptokeygeneratersacommand with the storagedevicename: keyword and argument, the RSA keys will bestored on the specified device. This location will supersede anycryptokeystoragecommand settings.
Specifying a Device for RSA Key Generation
As of Cisco IOS Release 12.4(11)T and later releases, you mayspecify the device where RSA keys are generated. Devices supportedinclude NVRAM, local disks, and USB tokens. If your router has aUSB token configured and available, the USB token can be used ascryptographic device in addition to a storage device. Using a USBtoken as a cryptographic device allows RSA operations such as keygeneration, signing, and authentication of credentials to beperformed on the token. The private key never leaves the USB tokenand is not exportable. The public key is exportable.
RSA keys may be generated on a configured and available USBtoken, by the use of the ondevicename: keyword and argument. Keys that reside on aUSB token are saved to persistent token storage when they aregenerated. The number of keys that can be generated on a USB tokenis limited by the space available. If you attempt to generate keyson a USB token and it is full you will receive the followingmessage:
Key deletion will remove the keys stored on the token frompersistent storage immediately. (Keys that do not reside on a tokenare saved to or deleted from nontoken storage locations when thecopyor similarcommand is issued.)
For information on configuring a USB token, see “ Storing PKICredentials ” chapter in the Cisco IOS Security ConfigurationGuide, Release 12.4T. For information on using on-token RSAcredentials, see the “ Configuring and Managing a Cisco IOSCertificate Server for PKI Deployment ” chapter in the Cisco IOSSecurity Configuration Guide , Release 12.4T.
Specifying RSA Key Redundancy Generation on aDevice
You can specify redundancy for existing keys only if they areexportable.
Crypto Key Generate Rsa
Examples
The following example generates a general-usage 1024-bit RSA keypair on a USB token with the label “ms2” with crypto enginedebugging messages shown:
Now, the on-token keys labeled “ms2” may be used forenrollment.
The following example generates special-usage RSA keys:
The following example generates general-purpose RSA keys:
Note | You cannot generate both special-usage and general-purpose keys;you can generate only one or the other. |
The following example generates the general-purpose RSA key pair“exampleCAkeys”:
The following example specifies the RSA key storage location of“usbtoken0:” for “tokenkey1”:

crypto key generate rsa general-keys label tokenkey1 storageusbtoken0:
The following example specifies the redundancy keyword:
Cisco Crypto Key Gen Rsa
The name for the keys will be: MYKEYS
Choose the size of the key modulus in the range of 360 to 2048for your
General Purpose Keys. Choosing a key modulus greater than 512may take
a few minutes.
How many bits in the modulus [512]:
% Generating 512 bit RSA keys, keys will be non-exportable withredundancy...[OK]
Related Commands
Cisco Generate Rsa Key
Command | Description |
|---|---|
copy | Copies any file from a source to a destination, use the copycommand in privileged EXEC mode. |
cryptokeystorage | Sets the default storage location for RSA key pairs. |
debugcryptoengine | Displays debug messages about crypto engines. |
hostname | Specifies or modifies the hostname for the network server. |
ipdomain-name | Defines a default domain name to complete unqualified hostnames(names without a dotted-decimal domain name). |
showcryptokeymypubkeyrsa | Displays the RSA public keys of your router. |
show crypto pki certificates | Displays information about your PKI certificate, certificationauthority, and any registration authority certificates. |
